CVE-2023-50224
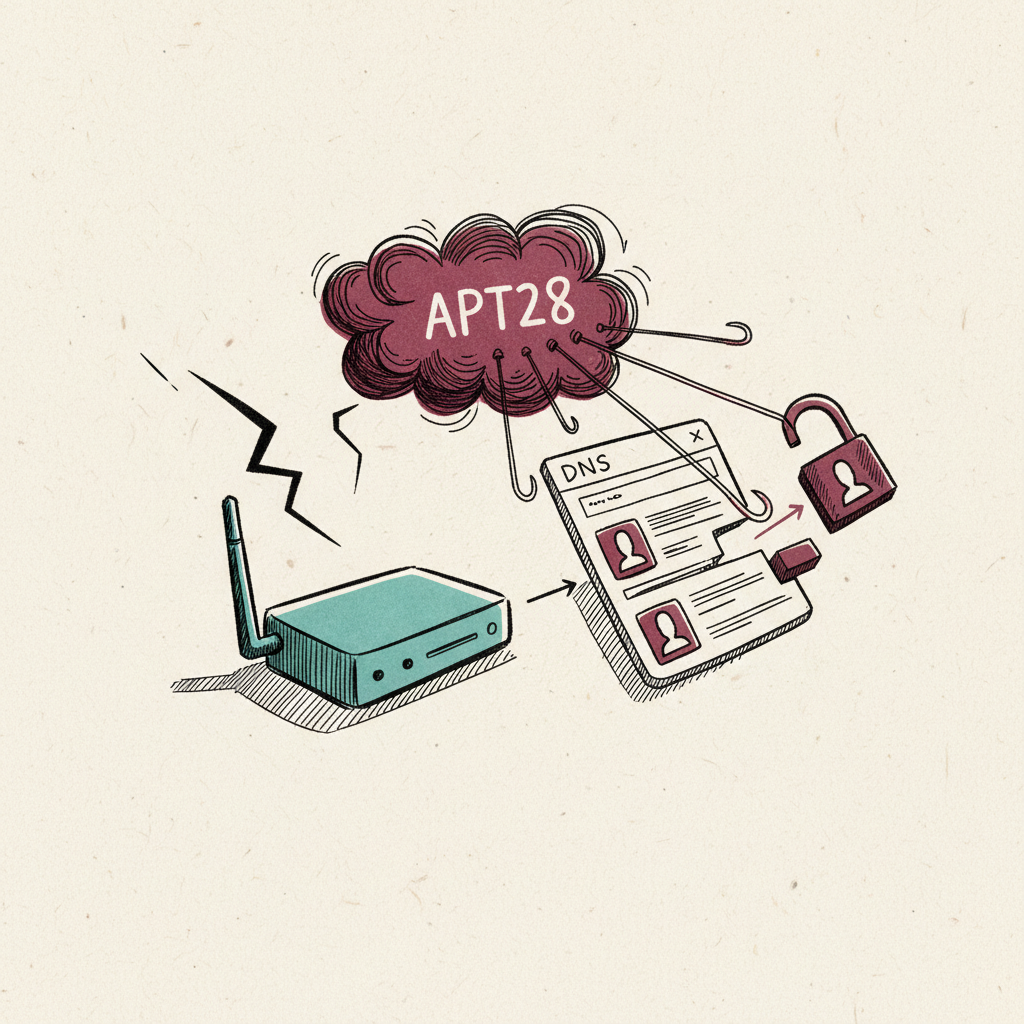
TP-Link WR841N router vulnerability exploited by APT28 to rewrite DNS settings and steal Microsoft 365 credentials.
Last refreshed: 20 May 2026 · Appears in 1 active topic
Why is a 2023 home-router flaw still giving Russia access to corporate Microsoft 365 accounts in 2026?
Timeline for CVE-2023-50224
Exchange repeats the CISA deadline-before-patch trap
Cybersecurity: Threats and DefencesMentioned in: Patch Tuesday clean streak hides out-of-band KEVs
Cybersecurity: Threats and DefencesUNC6780 takes Cisco AI Defense source code
Cybersecurity: Threats and DefencesAdded to KEV on 7 May with 10 May deadline, confirmed limited exploitation in the wild
Cybersecurity: Threats and Defences: Ivanti EPMM logs fourth KEV zero-day since 2023Disclosed by WatchTowr Labs and added to KEV on 30 April with 3 May deadline
Cybersecurity: Threats and Defences: cPanel zero-day ran 65 days before patch; Sorry ransomware active- What is CVE-2023-50224 and should I worry about it?
- CVE-2023-50224 is a vulnerability in TP-Link WR841N routers that Russia's APT28 has exploited since 2024 to intercept Microsoft 365 logins. If you have a WR841N, update its firmware and change the default admin password.Source: NCSC PSA260407
- How does APT28 use hacked home routers to steal Microsoft 365 passwords?
- APT28 exploits CVE-2023-50224 to gain access to the TP-Link WR841N admin panel and replaces the router's DNS resolver with an attacker-controlled server. All Microsoft 365 authentication traffic is redirected to the attacker's server, allowing credential and OAuth token harvesting without breaking the user's connection.Source: NCSC PSA260407
- Why are home routers still being used in state-level cyberattacks in 2026?
- Consumer routers are not managed on enterprise patch cycles. CVE-2023-50224 was published in 2023 and remains exploited in 2026: a three-year gap between disclosure and full remediation across deployed hardware. State actors target consumer devices because they provide persistent, low-cost network access to corporate accounts, with no endpoint detection coverage.Source: NCSC / Lowdown analysis
- Is the TP-Link WR841N router vulnerability fixed?
- A firmware update patching CVE-2023-50224 is available from TP-Link, but a large proportion of deployed WR841N devices run unpatched firmware with default admin credentials, which makes them accessible without exploiting the vulnerability itself. NCSC urges firmware update, credential change, and blocking admin-panel internet exposure.Source: NCSC PSA260407 / TP-Link
- What is the connection between CVE-2023-50224 and the Cisco SD-WAN and Exchange CVEs in 2026?
- All three are examples of the consumer-or-enterprise-router-as-attack-surface pattern. CVE-2023-50224 targets home routers to reach corporate accounts; Cisco SD-WAN CVE-2026-20182 (CVSS 10.0) and Exchange CVE-2026-42897 operate at the enterprise network and mail tiers. Each demonstrates that perimeter and edge devices, not just endpoint software, are the primary 2026 intrusion vectors.Source: CISA KEV catalogue
Background
CVE-2023-50224 is a vulnerability in the TP-Link WR841N consumer router that APT28 has exploited since 2024 to extract router credentials and modify DNS configuration for adversary-in-the-middle Microsoft 365 credential and OAuth token harvesting. The NCSC advisory published on 7 April 2026 identified the CVE as part of the attribution-backed GRU Unit 26165 campaign.
The vulnerability allows an unauthenticated attacker (or one with access to the router's admin panel, which on many home deployments uses default credentials) to extract sensitive configuration data and modify DNS settings. APT28 uses the access to replace the primary DNS resolver with an attacker-controlled server running dnsmasq on UDP 53, selectively routing only Microsoft 365 authentication domains to the attacker for credential interception. For home-router owners with affected models, NCSC's mitigation guidance is: update router firmware to the latest version, change default admin credentials, and avoid exposing the admin interface to the internet.
CVE-2023-50224 is a structural example of the consumer-router-as-enterprise-attack-surface pattern that recurs at every tier of the threat landscape. APT28's exploitation of a 2023-vintage consumer flaw on home hardware to reach corporate Microsoft 365 accounts sits in the same threat category as the Cisco SD-WAN CVE-2026-20182 (CVSS 10.0, exploited by UAT-8616 in May 2026) and the Exchange Server CVE-2026-42897 at the enterprise end of the same stack. The 2023 disclosure date and confirmed active exploitation in 2026 are evidence of the persistent patch gap in the consumer-router market: a three-year window between CVE publication and full remediation across deployed hardware, which state actors exploit precisely because consumer devices are not managed on enterprise patch cycles.