TP-Link WR841N
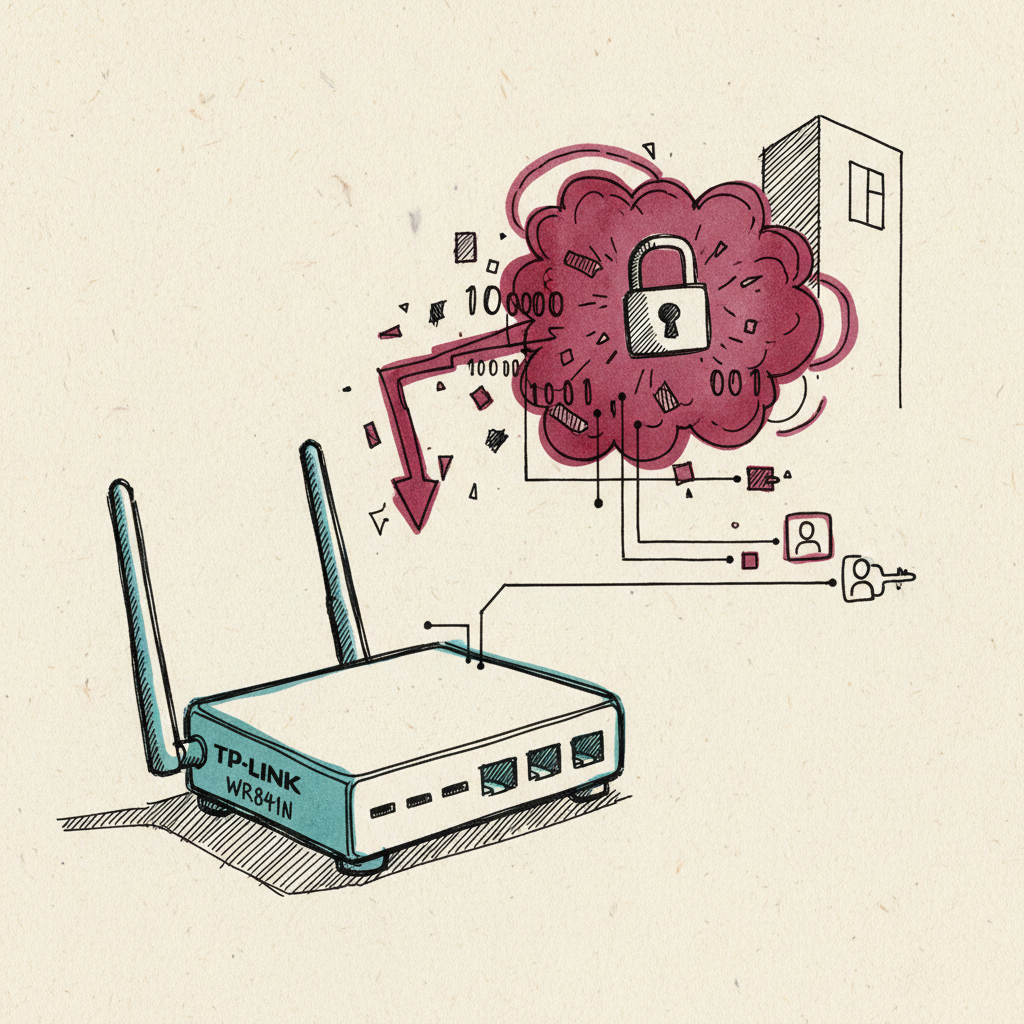
Consumer TP-Link router exploited by APT28 via CVE-2023-50224 for DNS hijacking to steal Microsoft 365 credentials.
Last refreshed: 17 April 2026 · Appears in 1 active topic
How can a cheap home router become a Russian intelligence collection point for corporate logins?
Timeline for TP-Link WR841N
GRU hijacks home routers for M365 logins
Cybersecurity: Threats and Defences- How did Russian hackers use home routers to steal Microsoft logins?
- APT28 exploited CVE-2023-50224 in TP-Link WR841N and other SOHO routers to rewrite DNS settings, routing Microsoft 365 login traffic through a GRU-controlled server for credential and OAuth token harvesting.Source: NCSC advisory PSA260407
- Is my TP-Link WR841N being used by Russian hackers?
- NCSC's April 2026 advisory identified the TP-Link WR841N as a device targeted by APT28. Mitigation is to update router firmware to the latest version and change default admin credentials immediately.Source: NCSC
Background
The TP-Link WR841N is a low-cost consumer SOHO router that APT28 (GRU Unit 26165) exploited via CVE-2023-50224 since 2024 to rewrite DNS settings for adversary-in-the-middle Microsoft 365 credential harvesting. The NCSC advisory published on 7 April 2026 identified the WR841N alongside other TP-Link models (WR840N, ARCHeR C7) and MikroTik devices as the hardware layer of the campaign.
The attack mechanism exploits CVE-2023-50224 to extract the router's credentials, then rewrites the primary DNS entry to an attacker-controlled server running dnsmasq-2.85, while keeping the secondary DNS legitimate. Only Microsoft's targeted domains resolve to the attacker; general browsing continues normally. The result is a highly targeted, invisible DNS interception that does not degrade the user's experience and produces no local indicator of compromise.
For enterprises with remote-working staff, the WR841N exemplifies the consumer-router risk class: millions of units deployed in home-working environments, rarely updated, with default admin credentials in many deployments. NCSC's guidance calls for firmware updates and changed default credentials as immediate mitigations; however, the operational reality for enterprise identity teams is that they cannot inventory or patch every router under a remote employee's desk.