Cloudflare Workers
Cloudflare's serverless platform whose legitimate traffic was exploited by UNC5221 as a BRICKSTORM command-and-control relay.
Last refreshed: 15 May 2026 · Appears in 2 active topics
How can you block BRICKSTORM malware if it hides behind Cloudflare's servers?
Timeline for Cloudflare Workers
Cut 1,100 employees on record revenue while citing 600% internal AI usage increase
AI: Jobs, Power & Money: Cloudflare cuts 1,100 on record revenue, cites AI surgeMentioned in: Upwork kills 25% of staff, declares team model dead
AI: Jobs, Power & MoneyMentioned in: PayPal phases 4,760 cuts to sidestep WARN Act
AI: Jobs, Power & MoneyBRICKSTORM dwell hits 393 days, Mandiant
Cybersecurity: Threats and Defences- How did Chinese hackers use Cloudflare to hide their malware?
- UNC5221 used Cloudflare Workers as a command-and-control relay for the BRICKSTORM backdoor. Because Workers traffic originates from Cloudflare's trusted IP ranges, standard blocklist-based network defences cannot distinguish it from legitimate use.Source: Mandiant M-Trends 2026
- What is Cloudflare Workers and how does it differ from AWS Lambda?
- Cloudflare Workers is a serverless computing platform that runs JavaScript and WebAssembly at the network edge, distributed across Cloudflare's global infrastructure. Unlike AWS Lambda, which runs in regional AWS data centres, Workers executes at 300+ edge locations close to end users, with no cold-start latency and a simpler pricing model. Both execute code on demand without managing servers.
- How did hackers abuse Cloudflare Workers for command and control?
- UNC5221 routed BRICKSTORM backdoor communications through Cloudflare Workers, generating HTTPS traffic from Cloudflare's legitimate IP ranges. Network defences cannot block Cloudflare IP space without disrupting thousands of legitimate applications, giving attackers an effectively uninspectable C2 channel. The technique is known as 'living off trusted infrastructure'.Source: Mandiant M-Trends 2026
- What are Cloudflare Workers used for?
- Workers are used for content delivery logic, API proxies, A/B testing, authentication, bot mitigation, and dynamic web applications at the edge. Developers write small JavaScript or WebAssembly scripts that run before requests reach origin servers. They are also increasingly used for AI inference at the edge.
- Why did Cloudflare cut 20% of its workforce while revenue was at record highs?
- Cloudflare CEO Matthew Prince said the cuts are 'not a cost-cutting exercise' but about defining how a high-growth company operates in the agentic AI era, citing a 600% internal AI usage surge in three months. Prince predicted Cloudflare would employ more people in 2027 than at any point in 2026.Source: Lowdown
Background
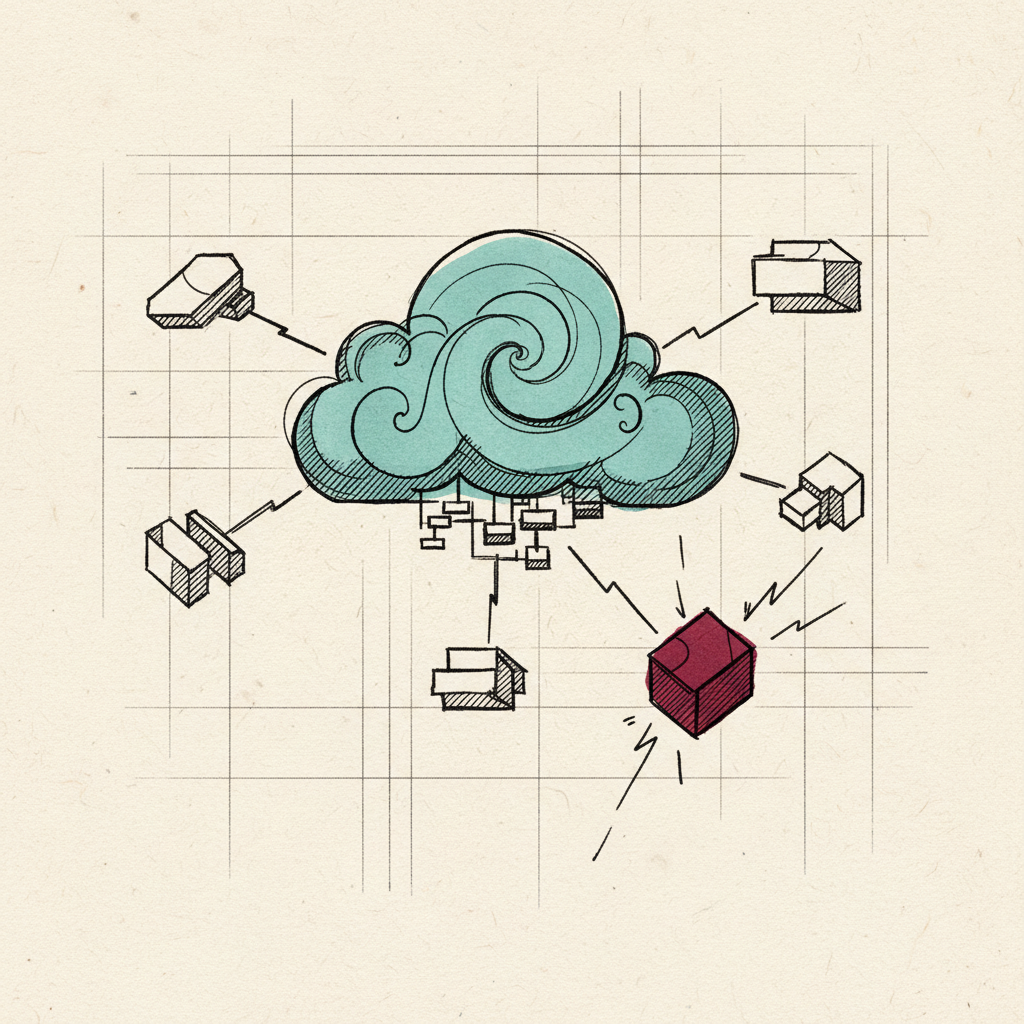
UNC5221 abused Cloudflare Workers, Cloudflare's serverless computing platform, as a command-and-control relay for the BRICKSTORM backdoor, according to Mandiant's M-Trends 2026 report. Because Workers generates traffic from Cloudflare's legitimate IP ranges and uses standard HTTPS, network-based blocklists designed to filter known-malicious infrastructure see normal cloud platform traffic.
Cloudflare Workers is a serverless execution environment that runs JavaScript and WebAssembly at the network edge. Its legitimate uses include content delivery, API proxies, and dynamic web applications. Its abuse as a C2 relay exploits the same properties that make it valuable: globally distributed, TLS-encrypted, originating from an IP space that is virtually impossible to block without disrupting legitimate traffic.
For security operations teams, the abuse of Cloudflare Workers alongside Heroku in the same campaign illustrates why blocklist-based defences are increasingly insufficient against sophisticated state-linked actors. The defensive response requires endpoint-level visibility into BRICKSTORM's process behaviour, not network-level filtering of Cloudflare IP ranges. The parent company, Cloudflare, cut 1,100 jobs (20% of workforce) in May 2026 on record quarterly revenue, citing a 600% internal AI usage surge — the platform itself is unaffected.